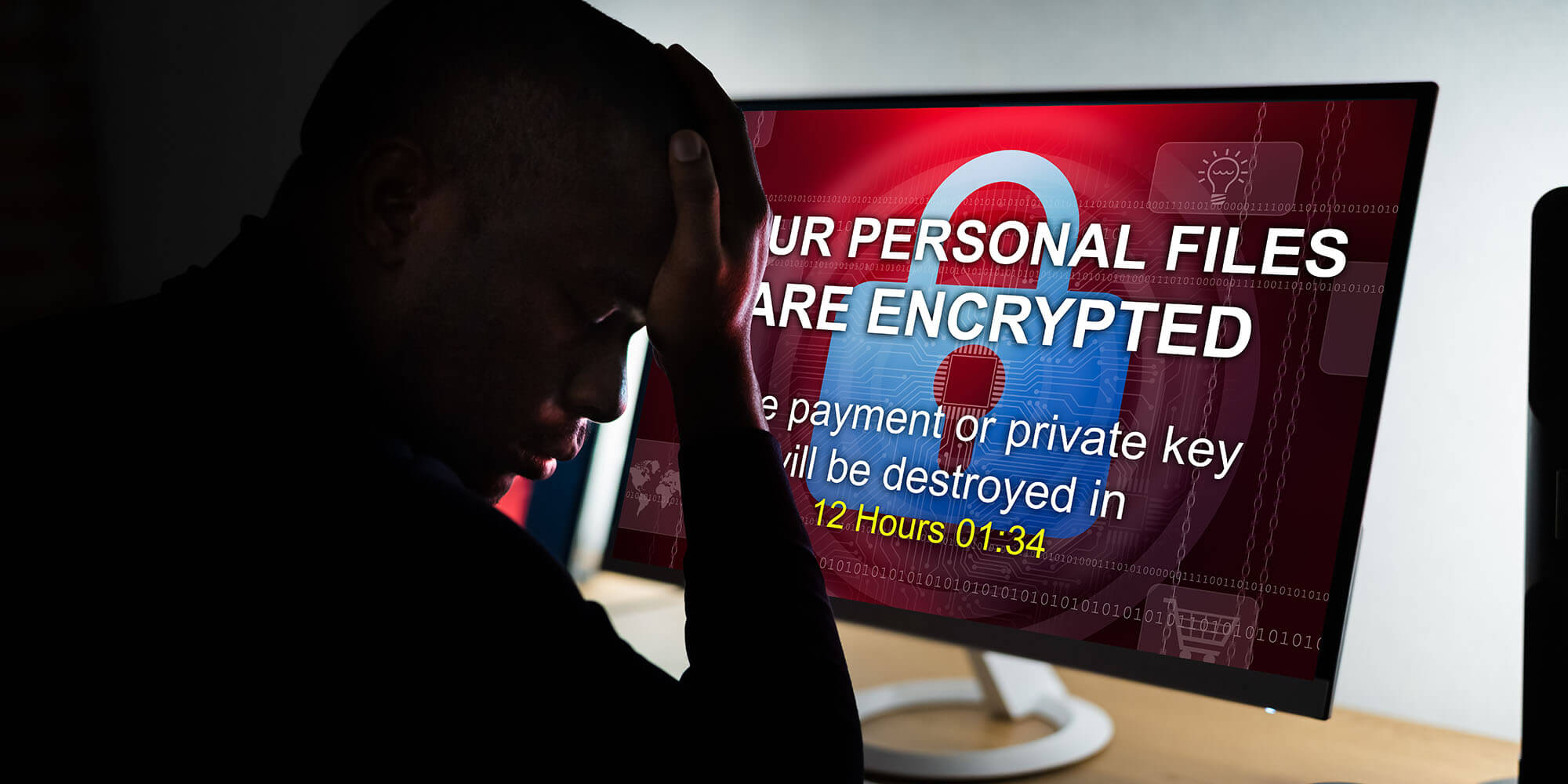
Ransomware.
It’s the latest tech phrase that’s all over the news headlines that many people may not understand what it actually is. The truth is that ransomware is a major threat to the stability and security of the internet, and attacks are getting worse.
What is it, and what can you, as an end-user, do to protect yourself?
A typical ransomware attack involves someone using malware (dodgy software) or known security exploits to access your network, computers, or IT infrastructure and then locking you out of it. To ‘unlock’ your stuff, they demand you pay them a ransom, almost always in Bitcoin or another cryptocurrency. If you refuse, they usually threaten to delete everything or keep you locked out forever.
The most recent Irish example is the recent attack on the Health Services Executive (HSE), which caused all of its IT systems nationwide to be shut down. Obviously, this happening in the middle of a pandemic was not ideal. The HSE shut down all their systems in order to figure out what to do. Since then, they’ve managed to decrypt most of the systems themselves without paying the ransom.
But many businesses and even governments around the world find that it’s easier to pay the ransom than to actually fix the problem. This has led to widespread attacks – such as the recent one on a pipeline provider in the USA that scared people into stockpiling gasoline (dangerously). Paying the ransom only encourages these attacks to continue.
Some businesses don’t want to publicise that they were attacked. Most of these attacks share the single thread – that payment must be made in Bitcoin or other cryptocurrencies because they’re anonymous and can’t be tracked (easily at least). Crypto is an efficient way to launder money.
So, what can you do to protect yourself in the event of a ransomware attack?
Keep everything updated – And we mean everything. Any computer connected to your network needs to be updated with the latest security patches at all times. Hackers will exploit known vulnerabilities, so it’s important to stay a step ahead of them. Be sure to update your servers, your computers, laptops, anything connected to a network.
Keep backups – You should always be backing up anyway. But also, it’s important to keep a backup that is offline as well – that way, if your systems get swept away or locked away in an attack, you can spin up the backups to restore operations as quickly as possible (though you would be wise to update the software in the backups as well to prevent the attack from happening all over again).
Have a plan to rebuild – So, worst-case scenario, you’ve been taken offline, and you refuse to pay the ransom. If you don’t have a backup – you still need to have a plan in place to completely rebuild your IT infrastructure to get back to operational levels again as quickly as possible. This is where an offline backup would come in handy.
Make passwords difficult – Simple passwords are the easiest thing for hackers to crack. Enforce strong password policies on your network – make users use a password generator and a password manager. The best passwords are at least 11 characters long, randomly generated, and made up of upper- and lower-case letters, symbols (such as a %, *, or >), and numbers. It’s less critical to enforce regular password changes – some cyber-security researchers say this is actually less secure as people tend to change it to a password they can easily remember (which is easier for bots to guess). And if any of your software supports it, enable two-factor authentication of some kind.
Train employees on phishing – One of the most common ways that hackers gain access is through phishing emails. Teach them how to spot fake emails. Check and verify senders. Put a warning on external email to be mindful of clicking any links. Sometimes all it takes is one wrong click for malware to get installed.
Install anti-virus software – Continual monitoring and maintenance is critical. All systems should have some kind of anti-virus software running at all times that can find problems and fix them before there is an issue. It can also help warn users from doing things they should not be doing that might be a security risk.
If it happens – You need to notify all stakeholders immediately. Starting with your IT and hosting providers. Then you need to notify your clients and then customers if people’s personal information has been accessed or compromised. Legal requirements will vary by country.
Ransomware attacks are not going anywhere – especially with the growing popularity of cryptocurrencies. So, it’s very important to be prepared for an attack and have a plan in place on how to deal with it. That way, if your critical infrastructure is taken offline, it doesn’t destroy your business or your reputation.